Most financial services firms understand their internal controls well. However, fewer have the same visibility into their vendors. Today, that gap is widening fast.
Vendor risk management has become a core financial discipline. CFOs can no longer treat third-party exposure as a back-office concern. Every vendor relationship now carries operational, regulatory, and financial weight.
The cost of getting it wrong continues to climb. Breaches involving third parties cost an average of $4.88 million per incident. Consequently, the boundary of accountability has moved well beyond the firm itself.
For finance leaders, this is no longer just a compliance question. Instead, it is a question of resilience, reputation, and capital efficiency. The choices made today will define how firms weather the next major incident.

Why Vendor Risk Management Matters More Than Ever
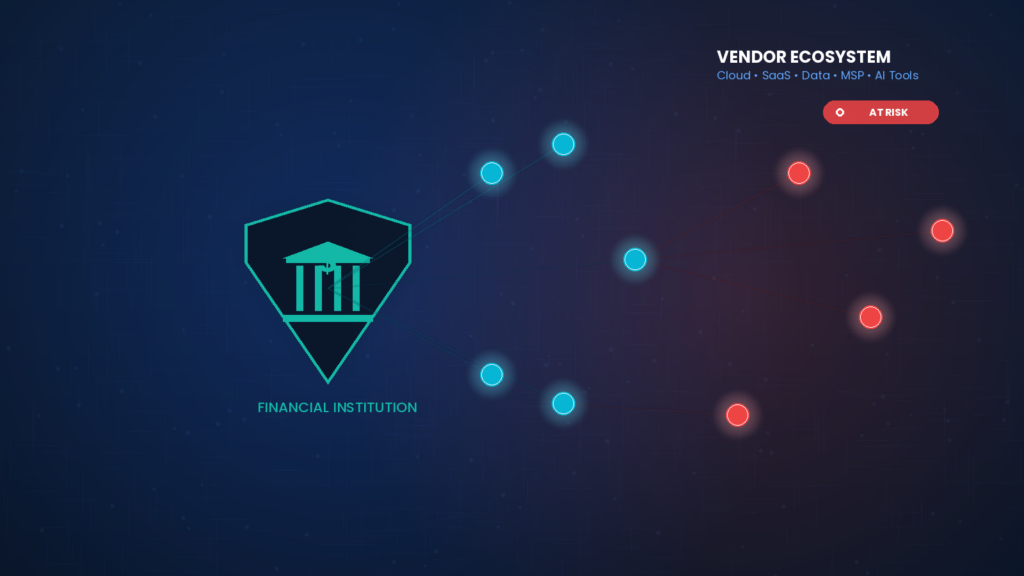
Modern financial services firms depend on a sprawling ecosystem of partners. Cloud platforms host critical data. SaaS applications run daily workflows.
Meanwhile, data providers feed analytics engines. Managed service providers operate core infrastructure. Each relationship introduces some level of access.
Vendors now reach into systems, data, and workflows. Over time, that access creates an extended attack surface. As a result, organizations face risks that exceed their direct visibility.
Third-party involvement in breaches has nearly doubled to roughly 30% of incidents. That trend signals a clear message. Therefore, vendor risk management cannot remain a periodic checklist exercise.
The Expanding Vendor Attack Surface
Vendors are no longer simple service providers. Today, they participate in core operations. Many process sensitive data daily.
Others automate critical workflows. Several integrate directly with internal systems. Meanwhile, vendors adopt AI and automation at varying speeds.
As a result, complexity grows in unpredictable ways. Risk now spreads across multiple organizations. Each one has its own controls, processes, and governance standards.
Consequently, a single weak link can affect dozens of firms downstream. CFOs must recognize this dynamic clearly. The financial implications of vendor compromise reach far beyond a single contract.
How Vendor Compromise Becomes a Financial Issue
When a vendor suffers a breach, the impact extends to every connected organization. Operational disruption can occur if a vendor service goes offline. Data exposure may follow if attackers reach sensitive information.
Regulatory obligations could trigger when customer data is involved. The financial consequences can be severe. Public disclosures and remediation costs add up quickly.
Furthermore, regulated industries face additional scrutiny from examiners. Accountability cannot be transferred to the vendor through a contract. Regulators expect the firm to own the outcome.
Why Traditional Approaches Fall Short
Most vendor management programs rely on periodic reviews. Teams complete questionnaires once a year. Compliance staff collect SOC 2 certifications.
Legal teams review contracts at renewal. This approach captures a snapshot in time. However, it does not reflect how risk evolves daily.
Vendors update systems constantly. They release new features, expand integrations, and shift architectures. As a result, the risk profile changes between formal reviews.
Without continuous visibility, firms react instead of manage. That delay creates exposure. Therefore, CFOs need a vendor risk management approach that matches the speed of modern operations.
How AI and Automation Reshape Third-Party Risk
AI adoption among vendors introduces new dimensions of exposure. Many vendors now embed machine learning into their products. Some use customer data to train models.
Others connect to systems that handle sensitive financial information. Without clear governance, these capabilities can create unintended data flows. Moreover, AI features often launch faster than security reviews can keep pace.
Therefore, CFOs should ask specific questions about vendor AI use. How is data isolated? Who has access to model outputs? What controls limit model behavior?
These questions belong inside every modern vendor risk management program. They protect the firm from emerging threats that traditional reviews miss entirely.
Building a Modern Vendor Risk Management Framework
Effective vendor risk management requires a fundamental shift in approach. The framework starts with prioritization and ends with continuous oversight. Below are the core elements every CFO should expect from a modern program.
A strong framework treats vendors as part of the firm’s operating environment. Therefore, it applies the same rigor used for internal controls.
Identify and Prioritize Critical Vendors
Not every vendor carries the same level of risk. First, classify vendors based on their access to sensitive data and core operations. Tier-one vendors touch customer data or run essential workflows.
Tier-two vendors support secondary functions. Tier-three vendors have minimal access. Then, focus oversight where it matters most.
The NIST Cybersecurity Framework offers useful guidance on supply chain risk tiering. This approach prevents teams from spreading effort too thin. It also makes board-level reporting more meaningful and credible.
Map Data Flows Across Vendor Systems
Next, understand how data moves through your vendor environment. Document where data is stored, processed, and protected. Identify which vendors hold personally identifiable information.
Track which platforms exchange data with each other. Without this visibility, incident response becomes guesswork. Moreover, regulators increasingly expect documented data flow diagrams.
The SEC’s cybersecurity disclosure rules reinforce this expectation. Mapping data flows transforms vendor risk management from theory into practice.
Strengthen Contractual Requirements
Contracts must do more than allocate cost and scope. Today, they should define security obligations clearly. Include incident notification timelines, often within 24 to 72 hours.
Specify cooperation requirements during investigations. Require evidence of ongoing security controls. Define audit rights and remediation expectations.
Additionally, contracts should address subcontractor risk directly. Many breaches originate not with the primary vendor but with their suppliers. Therefore, strong contractual language anchors effective vendor risk management.
Establish Continuous Monitoring
Periodic reviews alone cannot keep pace with modern threats. Instead, firms should monitor vendor risk continuously. Track changes in vendor environments and ownership.
Review access controls regularly. Validate that security practices remain aligned with expectations. Several platforms now offer real-time vendor security ratings.
These tools complement traditional questionnaires effectively. As a result, leadership gains a current view of third-party exposure. Continuous monitoring is the most significant evolution in vendor risk management today.
Coordinating Incident Response Across Vendors
When a vendor incident occurs, speed determines damage. The first 24 hours often shape the entire response. However, many firms discover gaps in their playbooks only during a real event.
Build incident response procedures with vendors in mind. Identify primary contacts for every critical vendor. Document escalation paths in advance. Then, test the process through tabletop exercises at least annually.
Likewise, establish clear communication protocols for regulators and customers. Pre-approved messaging reduces confusion under pressure. Coordination with vendor counsel and forensics teams must happen quickly.
Strong incident response planning makes vendor risk management actionable. It transforms a paper program into a living capability.
The Regulatory Pressure Continues to Intensify
Regulators across jurisdictions are sharpening their focus on third-party risk. New rules demand faster disclosure and deeper documentation. Examiners increasingly probe vendor oversight during audits.
The FFIEC’s IT examination guidance places direct responsibility on financial institutions. Likewise, the New York Department of Financial Services requires extensive third-party security controls. Europe’s Digital Operational Resilience Act adds another layer for global firms.
Each new framework reinforces a single principle. The vendor’s controls do not absolve the firm. Therefore, vendor risk management programs must mature alongside the regulatory environment.
The Shift to Shared Accountability
Vendor risk is often described as a shared responsibility. However, accountability remains with the contracting organization. Regulators expect firms to manage risks tied to their vendors.
Customers expect the same. Stakeholders demand it. This expectation elevates vendor risk management to a board-level financial issue.
It affects operational continuity. It influences regulatory compliance. Likewise, it shapes brand trust and long-term enterprise value.
Boards now ask harder questions about third-party oversight. They want clear answers backed by documented evidence. CFOs play a central role in providing that clarity.
Why Vendor Risk Management Is a CFO Priority
For CFOs, vendor risk is not an abstract concern. It directly affects the organization’s ability to operate, report, and maintain trust. As vendor ecosystems expand, the risk grows accordingly.
Therefore, managing that risk requires the same discipline applied to internal controls. The boundary of the organization is no longer defined by its own systems. Today, it is defined by everything the firm depends on.
Modern vendor risk management aligns financial oversight with operational reality. CFOs who lead this shift position their firms to grow with confidence. They also strengthen credibility with regulators, investors, and clients.
Coretelligent’s cybersecurity and compliance solutions help financial services leaders operationalize stronger third-party oversight. Our financial services IT solutions align vendor governance with regulatory expectations.
Moving Forward With a Stronger Approach
The path to stronger vendor risk management starts with honest assessment. Where does your firm stand today? Which vendors have the deepest access?
How quickly would you know if one of them was compromised? These questions guide the next steps. Building a mature program takes time and discipline.
However, every improvement reduces exposure measurably. Partner with experienced advisors who understand financial services. Choose tools that scale with your environment as it grows.
Most importantly, treat vendor risk management as a continuous discipline. Explore our perspective on cybersecurity governance and compliance in the age of mega breaches for additional context. The firms that lead today will be the ones still standing when the next major incident hits.
